Before You Begin
Make sure you have:- Database hostname, port, and credentials
- Network access from AnomalyArmor to your database (see Quickstart Overview)
- A read-only database user (recommended)
Supported Databases
| Database | Version | Notes |
|---|---|---|
| PostgreSQL | 12+ | Including RDS, Aurora, Supabase |
| Databricks | Unity Catalog | Requires access token |
| ClickHouse | 21+ | Including ClickHouse Cloud |
Step-by-Step Guide
Navigate to Asset Management
From the AnomalyArmor dashboard, click Settings in the left sidebar, then select the Assets tab.You’ll see the Asset Management page with a list of your existing connections (empty if this is your first time).
Click Add New Asset
Click the Add New Asset button. You can find this button in the top right corner of the page, or in the center of the page if you have no assets configured yet.
Select Database Type
Choose your database type from the available options:
- PostgreSQL - For PostgreSQL, Amazon RDS, Aurora, Supabase, etc.
- Databricks - For Databricks with Unity Catalog
- ClickHouse - For ClickHouse or ClickHouse Cloud
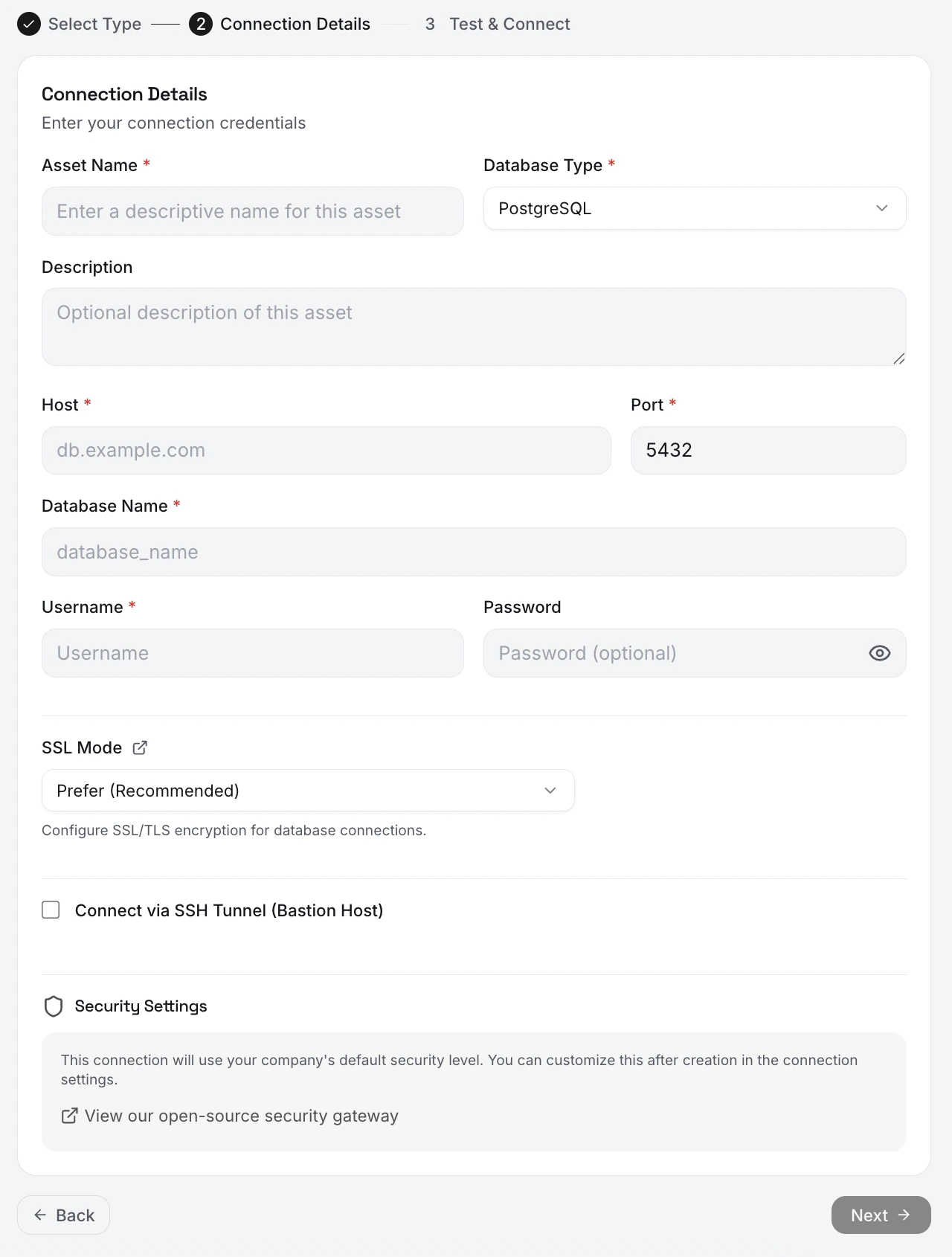
Enter Connection Details
Fill in your connection information:
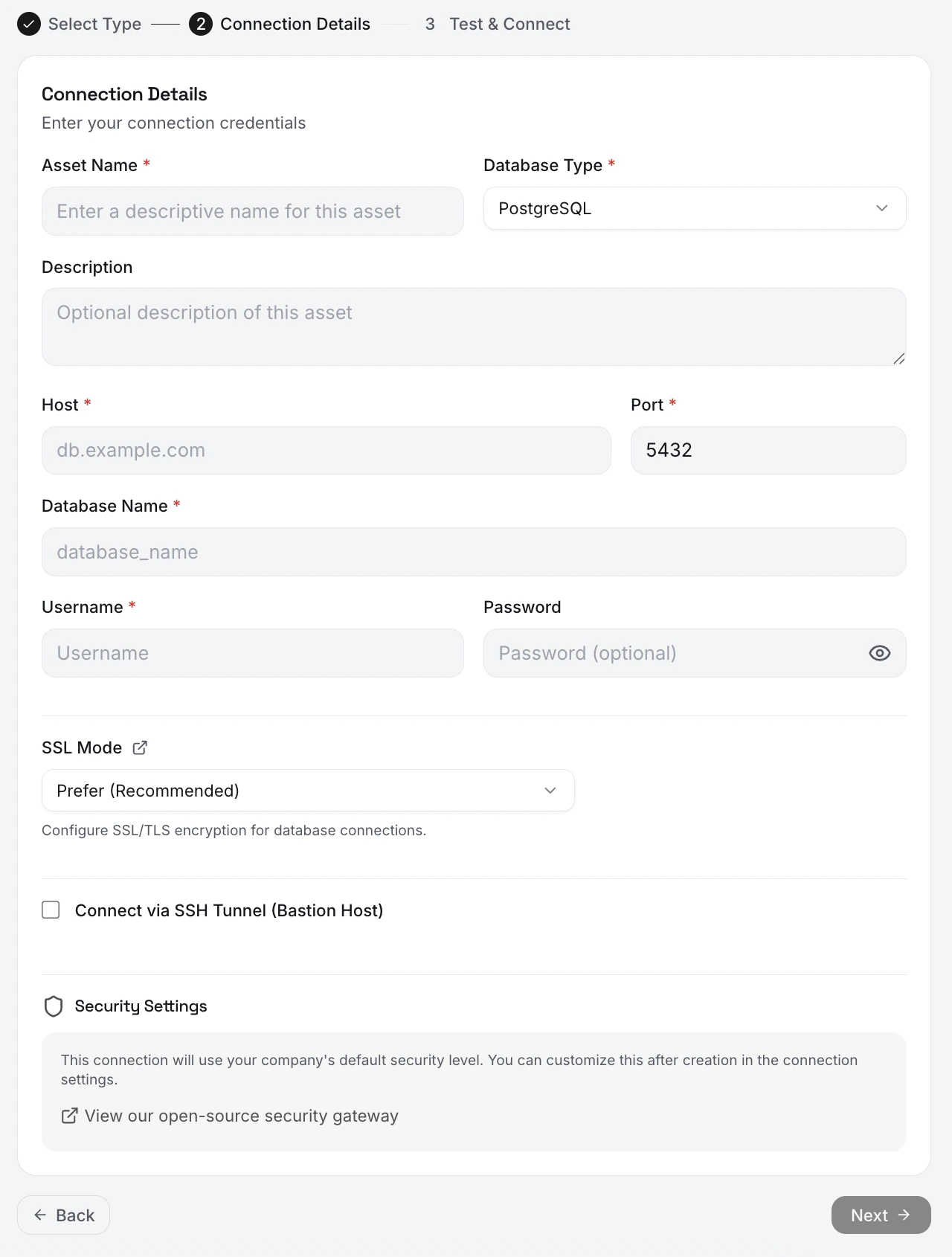
- PostgreSQL
- Databricks
- ClickHouse
| Field | Description | Example |
|---|---|---|
| Connection Name | A friendly name for this connection | Production PostgreSQL |
| Host | Database hostname or IP | db.example.com |
| Port | Database port | 5432 |
| Database | Database name | production |
| Username | Database user | anomalyarmor_reader |
| Password | User password | •••••••• |
| SSL Mode | SSL configuration | require (recommended) |
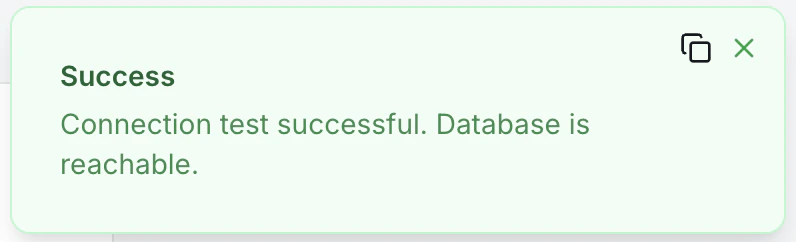
Test Connection
Click Test Connection to verify AnomalyArmor can reach your database.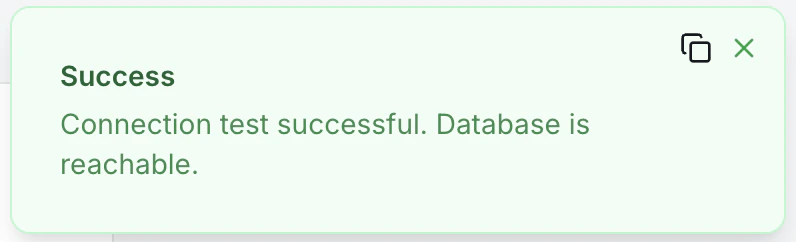
What Happens Next
After saving your connection:- Credentials are encrypted: Stored securely with AES-256 encryption
- Connection is ready: You can now run discovery to scan your database
- No data accessed yet: Discovery must be triggered manually or scheduled
Security Best Practices
Creating a Read-Only User
- PostgreSQL
- ClickHouse
- Databricks
Troubleshooting
Connection refused
Connection refused
Cause: Network connectivity issuesSolutions:
- Verify the hostname and port are correct
- Check that your database is running
- Ensure AnomalyArmor IPs are allowlisted in your firewall/security group
- For RDS: Verify the security group allows inbound traffic on your DB port
Authentication failed
Authentication failed
Cause: Invalid credentialsSolutions:
- Double-check username and password (copy-paste to avoid typos)
- Verify the user exists in the database
- Ensure the user has CONNECT permission on the database
- Check for special characters in password that may need escaping
SSL connection required
SSL connection required
Cause: Database requires SSL but connection isn’t using itSolutions:
- Set SSL Mode to
requirein the connection form - For RDS: SSL is required by default, ensure SSL Mode is set
- For self-hosted: Verify SSL certificates are properly configured
Connection timeout
Connection timeout
Cause: Network latency or firewall issuesSolutions:
- Verify the database is accessible from outside your VPC
- Check for firewall rules blocking the connection
- For private databases: Contact us about VPC peering options
Permission denied
Permission denied
Cause: User lacks required permissionsSolutions:
- Grant
SELECToninformation_schematables - Grant
USAGEon the schema you want to monitor - Verify user can access the specific database
Next Step
Your database is connected! Now let’s discover your tables and schemas.Run First Discovery
Scan your database to catalog tables, views, and columns
